Your one-stop guide to using Python, creating your own hacking tools, and making the most out of resources available for this programming languageAbout This Book• Comprehensive information on building a web application penetration testing framework using Python• Master web application penetration testing using the multi-paradigm programming language Python• Detect vulnerabilities in a system or application by writing your own Python scriptsWho This Book Is ForThis book is for ethical hackers; penetration testers; students preparing for OSCP, OSCE, GPEN, GXPN, and CEH; information security professionals; cybersecurity consultants; system and network security administrators; and programmers who are keen on learning all about penetration testing.What You Will Learn• Code your own reverse shell (TCP and HTTP)• Create your own anonymous shell by interacting with Twitter, Google Forms, and SourceForge• Replicate Metasploit features and build an advanced shell• Hack passwords using multiple techniques (API hooking, keyloggers, and clipboard hijacking)• Exfiltrate data from your target• Add encryption (AES, RSA, and XOR) to your shell to learn how cryptography is being abused by malware• Discover privilege escalation on Windows with practical examples• Countermeasures against most attacksIn DetailPython is an easy-to-learn and cross-platform programming language that has unlimited third-party libraries. Plenty of open source hacking tools are written in Python, which can be easily integrated within your script.This book is packed with step-by-step instructions and working examples to make you a skilled penetration tester. It is divided into clear bite-sized chunks, so you can learn at your own pace and focus on the areas of most interest to you. This book will teach you how to code a reverse shell and build an anonymous shell. You will also learn how to hack passwords and perform a privilege escalation on Windows with practical examples. You will set up your own virtual hacking environment in VirtualBox, which will help you run multiple operating systems for your testing environment.By the end of this book, you will have learned how to code your own scripts and mastered ethical hacking from scratch.Style and approachThis book follows a practical approach that takes a gradual learning curve, building up your knowledge about ethical hacking, right from scratch. The focus is less on theory and more on practical examples through a step-by-step approach.
- 176 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Python for Offensive PenTest
About this book
Trusted by 375,005 students
Access to over 1 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Warming up – Your First Antivirus-Free Persistence Shell
Nowadays, security solutions such as firewalls, IPS, and sandboxing are becoming more and more advanced to prevent and detect cyber-attacks. So, being an advanced hacker requires you to code your own script and tools to bypass these security solutions.
The following topics will be covered in this chapter:
- Preparing the attacker machine
- Preparing the target machine
- TCP reverse Shell
- HTTP reverse Shell
- Persistence
- Tuning connection attempts
- Tips for preventing a shell breakdown
- Countermeasures
Preparing the attacker machine
In this section, we will prepare our Kali Linux machine as the attacker. Note that we are assuming that the operating system is already set up in VMware or VirtualBox. As of now, we will be using VirtualBox for all our chapters.
We can check the version of any Linux OS by running the following cat command to display the content from the file /etc/os-release, which contains OS distribution data. We will be using Kali Linux version 2018.1, as you can see from the following screenshot:

It doesn't matter what your Kali version is. For this book, we will be using the latest version available at the time of writing. Since, by default, Python is preinstalled in every Linux distribution, we can get the version details from either the interactive shell by running the command python or by using python -V, as shown in the following screenshot:

We will be using Python 2.7.14+ for now, which came preinstalled with our Linux version.
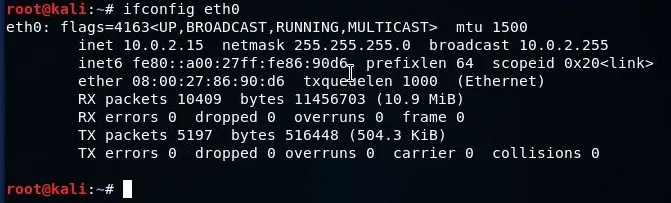
So, let's go for networking a little bit. In this chapter, the Kali IP is 10.0.2.15. We can check the Kali IP by running the ifconfig eth0 command. This will return the network interface configuration as shown here:
Setting up internet access
To set up the internet on our system, we just need to change the network mode to Network Address Translation (NAT) in VirtualBox. NAT mode will mask all network activity as if it came from your host OS, although VirtualBox can access external resources. To do this, perform the following steps:
- Click on the Devices menu from VirtualBox's menu bar
- Go to Network and select Network Settings
- Select the network mode as NAT and click on OK as shown in the following screenshot:

Once you perform the preceding steps, you should be able to reach the internet, as long as the VirtualBox host does. You can check internet access by running ping 8.8.8.8 from the terminal.
Now, if you don't have a GUI compiler for Python, you can just install it using the following command:
apt-get install idle
Once it's installed, let's do a quick print program using IDLE (using Python-2.7), which we installed using the previous command. Open a new Python file and type print ('hello there'). Run the program and save it on the desktop. Once you finish accessing the internet, you now need to change the network mode back to Internal Network so that we can reach out to our Windows target. This is shown in the following screenshot:
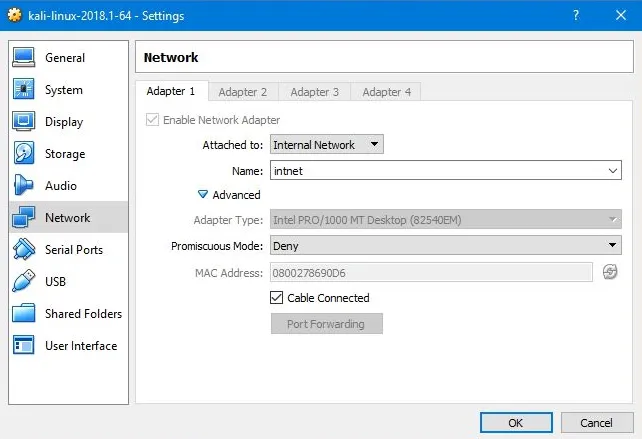
Note that the Windows target globally machine is sitting on the same internal network as Kali attacker globally machine, intnet, here.
And, as a last step, we should verify that we still got the same IP address, which is 10.0.2.15 by running ifconfig in the terminal.
if the IP changes, you can change the IP back by running ifconfig eth0 10.0.2.15.
Preparing the target machine
In this section, we will be preparing our target. We are using a 32-bit Windows 7 machine as our target. We will begin by installing Python 2.7.14+ version from https://www.python.org/downloads/. After you begin the installation, you'll notice that Python will install other handy tools such as pip and easy_install. We will be using pip to install third-party libraries later on.
Similar to what we have done in Kali, we will create a quick and simple Python script just to make sure that everything is working fine. Create a new file. Type print ('hi'), run the script, and save it to the desktop. After this, we need to add Python to our path, so we can start an interactive mode or interactive shell anywhere from the command line. Open a command line and type python; you will see that Windows does not recognize the python.exe application by default, so we've got to add that manually.
Perform the following steps to achieve this:
- Go to Advanced system settings | Environment Variables.
- In System Variables, scroll down until you reach the variable Path. You will need to append the Python path and the pip path here.
- Copy the path where the Python application is installed and append it to the Variable value.
- Ensure that you insert a semicolon at the end, just to make sure that you append it to our existing Variable value.
- Also, copy the path where pip is installed from the /Scripts folder and append it to the Variable value as shown in the following screenshot:

- Restart the machine so that it recognizes the new values we've just inserted.
- After the restart is complete, open a command line and type python and the interactive shell will appear:

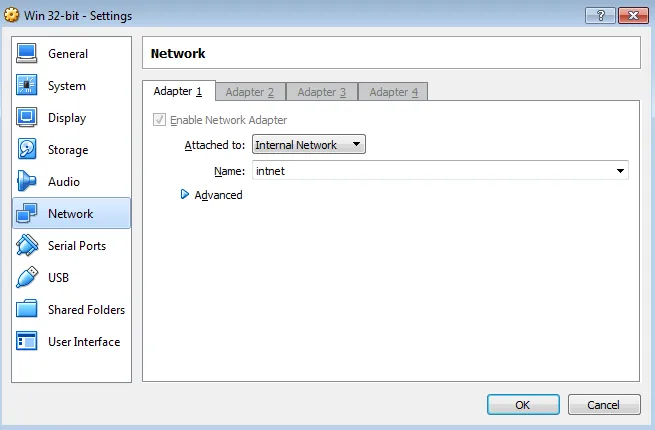
- Now, to get connectivity with our Kali machine, make sure that the network setting is set to Internal Network and the network name matches the name on the Kali side, which is intnet:
- Lastly, we need to give this machine an IP address on the same subnet as the Kali machine. We can change the network settings by going to Network and Internet/Network and Sharing Center from the control panel. Click on the Local Area Connection and then click on Properties. From there, go to Internet Protocol Version 4 (TCP/IPv4), enter the IP address as 10.0.2.10 and the rest as shown in the following screenshot. Then click on OK:

We have installed the Python compiler on the target machine just to have a better way to explain the code and compile it. However, we will compile the Python script into a standalone EXE later on, so it'll work on any target without having a Python compiler installed.
TCP reverse shell
In this section, we will have a quick overview of TCP reverse shells, why we need a reverse connection, and what a shell is. The best way to answer these questions is to study the topology shown in the following figure:

Let's say that we have an Attacker connected somewhere on the Internet, and on the right side we have our Target. So technically, we have a PC that is fully patched with a built-in firewall enabled, and we have the corporate firewall in place. And most likely that Corporate firewall is integrated with an IPS module or Antivirus software. So now, for the attacker to access this protected PC, there are two major problems here. First, the attacker needs to bypass the built-in or the host-based firewall on the operating system, which, by default, will block any incoming connection to that PC unless it's explicitly permitted; and the same rule goes for the corporate firewall as well.
But, if the attacker could somehow find a way to send a malicious file to the user, or maybe trick that user into visiting our malicious website and downloading a malicious file, then we might be able to compromise that PC or maybe the whole network. So, in order to bypass the firewall root restriction, we need to make our target, which is the TCP client, initiate the connection back to us. So, in this case, we are acting as a TCP server, and our target, or our victim here, is acting as a TCP client and this is exactly why we need a reverse shell.
Now, we need to understand what a shell is in the first place. If we can initiate a cmd process on the target machine and bind that process to a network socket, in this case, it's called a reverse shell. Hence, when we say ...
Table of contents
- Title Page
- Copyright and Credits
- Packt Upsell
- Contributors
- Preface
- Warming up – Your First Antivirus-Free Persistence Shell
- Advanced Scriptable Shell
- Password Hacking
- Catch Me If You Can!
- Miscellaneous Fun in Windows
- Abuse of Cryptography by Malware
- Other Books You May Enjoy
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Python for Offensive PenTest by Hussam Khrais in PDF and/or ePUB format, as well as other popular books in Computer Science & Cyber Security. We have over one million books available in our catalogue for you to explore.