Building and securely deploying container-based applications with Docker and Kubernetes using open source tools.
Key Features
? Real-world examples of vulnerability analysis in Docker containers.
? Includes recommended practices for Kubernetes and Docker with real execution of commands.
? Includes essential monitoring tools for Docker containers and Kubernetes configuration.
Description
This book discusses many strategies that can be used by developers to improve their DevSecOps and container security skills. It is intended for those who are active in software development. After reading this book, readers will discover how Docker and Kubernetes work from a security perspective.
The book begins with a discussion of the DevSecOps tools ecosystem, the primary container platforms and orchestration tools that you can use to manage the lifespan and security of your apps. Among other things, this book discusses best practices for constructing Docker images, discovering vulnerabilities, and better security. The book addresses how to examine container secrets and networking. Backed with examples, the book demonstrates how to manage and monitor container-based systems, including monitoring and administration in Docker.
In the final section, the book explains Kubernetes' architecture and the critical security threats inherent in its components. Towards the end, it demonstrates how to utilize Prometheus and Grafana to oversee observability and monitoring in Kubernetes management.
What you will learn
? Familiarize yourself with Docker as a platform for container deployment.
? Learn how Docker can control the security of images and containers.
? Discover how to safeguard and monitor your Docker environment for vulnerabilities.
? Explore the Kubernetes architecture and best practices for securing your Kubernetes environment.
? Learn and explore tools for monitoring and administering Docker containers.
? Learn and explore tools for observing and monitoring Kubernetes environments.
Who this book is for
This book is intended for DevOps teams, cloud engineers, and cloud developers who wish to obtain practical knowledge of DevSecOps, containerization, and orchestration systems like Docker and Kubernetes. Knowing the fundamentals of Docker and Kubernetes would be beneficial but not required.
Table of Contents
1. Getting Started with DevSecOps
2. Container Platforms
3. Managing Containers and Docker Images
4. Getting Started with Docker Security
5. Docker Host Security
6. Docker Images Security
7. Auditing and Analyzing Vulnerabilities in Docker Containers
8. Managing Docker Secrets and Networking
9. Docker Container Monitoring
10. Docker Container Administration
11. Kubernetes Architecture
12. Kubernetes Security
13. Auditing and Analyzing Vulnerabilities in Kubernetes
14. Observability and Monitoring in Kubernetes
eBook - ePub
Implementing DevSecOps with Docker and Kubernetes
An Experiential Guide to Operate in the DevOps Environment for Securing and Monitoring Container Applications (English Edition)
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Implementing DevSecOps with Docker and Kubernetes
An Experiential Guide to Operate in the DevOps Environment for Securing and Monitoring Container Applications (English Edition)
About this book
Trusted by 375,005 students
Access to over 1.5 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Subtopic
Cyber SecurityIndex
Computer ScienceCHAPTER 1
Getting Started with DevSecOps
In this chapter, we will review DevSecOps challenges, methodologies, and tools as a new movement that tries to improve the security of applications. The idea of DevSecOps is to take security as a requirement in the application design, development, and delivery processes.
Structure
We will cover the following topics in this chapter:
- From DevOps to DevSecOps
- Getting started with DevSecOps
- DevSecOps methodologies
- Continuous integration and continuous delivery
- DevSecOps tools
Objectives
After studying this chapter, you will be able to understand the concepts of DevOps and DevSecOps. You will also understand DevSecOps methodologies, grasp the concepts of continuous integration and continuous delivery, and learn about DevSecOps tools.
From DevOps to DevSecOps
Today, DevOps allows organizations to deploy changes to production environments at faster speeds without comparing them to classic methodologies. Basically, it’s a set of practices that combines the development and IT operations teams with the aim of shortening software development life cycle with CI/CD practices. A DevOps process would have the following phases:
- A developer writes the code using the development environment of their choice and uploads it to a centralized code repository like Git or Bitbucket.
- The Continuous Integration (CI) server downloads the source code from the central repository and packages the built artifacts and binaries. For example, Docker images are created and pushed to the Docker registry for containerized applications.
- These artifacts and binaries are downloaded from the repository to be deployed in different pre-production and production environments, where they are built using container technologies like Docker and Kubernetes.
- Containers are built from the Docker images. If the environment is not a containerized one (like VMs), sometimes the process is just copying the binaries to a drop location.
From a security point of view, DevOps could include a number of best practices that can be applied to increase the security of applications. These best practices include the following:
- Add automated security testing techniques, such as fuzz test and software penetration testing, to the software development lifecycle or system integration cycle
- Standardization of the integration cycle to reduce the introduction of errors
- Introduction of security issues and limitations to software and systems development teams at startup of the projects
At this point, we can introduce DevSecOps as a methodology that aims to integrate security tools into the DevOps process in an automated way.
This necessarily leads to a cultural change in the normal operation of DevOps, and teams must be trained so that they understand what tools they have at their disposal, what they can achieve, and how they work, which allows efficient collaboration between teams, creating a robust security culture in the organization and development teams.
As a result, this multicultural and multidisciplinary automated security environment makes security an issue that affects everyone and not just a single team. This is one of the main engines of DevSecOps.
The following image shows how we are introducing security in DevOps:
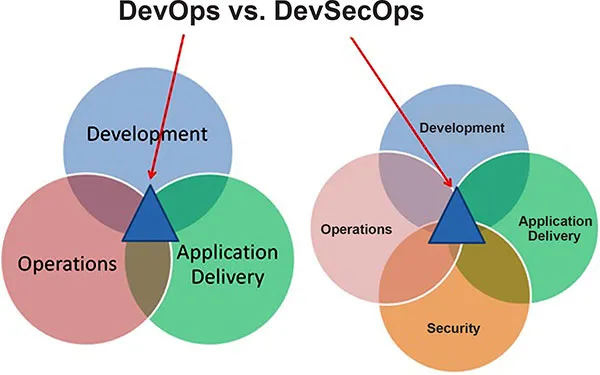
Figure 1.1: DevOps vs DevSecOps
Getting started with DevSecOps
The speed at which organizations want to launch software products, especially with DevOps, needs you to have the right tools and processes in the right place. It is in those cases that DevSecOps brings greater value to organizations by incorporating privacy and security into DevOps practices, while allowing you to continue operating with an enhanced level of cybersecurity.
DevSecOps is an initiative that aims to adopt security practices to include them in the DevOps process. Gartner provides a more precise definition: ”DevSecOps is the integration of security in DevOps development in the most fluid and transparent way possible. Ideally, this is done without reducing the agility or speed of developers or without requiring developers to change their tools in the development environment.”
These are the practices of how DevSecOps is implemented:
- Integrate security tools in the development integration process
- Prioritize security requirements as part of the product’s backlog
- Collaborate with the security and development teams on the threat model
- Review infrastructure-related security policies prior to deployment
In those circumstances, applying a DevSecOps methodology is the best option for organizations as it incorporates best practices into the core of the software product development cycle. It does this by integrating security practices into all areas of software development, from infrastructure and continuous integration to deployments and continuous delivery of applications.
In addition, applications should follow information security best practices, including issues like data integrity, availability, and confidentiality, helping developers become aware of how to code in a secure way and the need to understand security best practices.
Advantages of implementing DevSecOps
The DevSecOps philosophy makes all team members, regardless of whether a security is their specialty, aware of the need to apply best practices in this matter.
All this will contribute to adding value to the projects carried out. They are not only intended to be functional and easy to use, but security is taken into account as an element of the development process to create secure code. This will allow vulnerabilities to be detected faster and improve responsiveness and patching to any security threat.
Here are some of the benefits of implementing DevSecOps:
- Early identification of potential vulnerabilities in the code is encouraged.
- Greater speed and agility in applying security in all phases of development.
- Throughout the development process, tools and mechanisms are provided to quickly and efficiently respond to changes and new requirements.
- Better collaboration and communication between teams involved in development, as in DevOps.
In this way, tasks related to application security can be subject to automation and monitoring mechanisms if security elements are integrated from the early stages of development.
In addition, the different teams in charge of development and operations become familiar with the security factors and apply them from the beginning, preventing possible security breaches. So, secure and stable versions of software are created in a short time, and these can be made directly available to customers. This means both customers and organizations benefit from the new possibilities.
DevSecOps lifecycle
Just like DevOps proposes the integration of tools to ensure the correctness of the code throughout the development cycle, DevSecOps suggests the integration of security tools as part of the continuous integration and deployment processes.
The integration of these tools make up pipelines known as application security pipelines, which can be abbreviated as app sec pipelines. These pipelines may include phases like code review automation, security testing, security scans, monitoring, and automated report generation.
This is the lifecycle and the flow of different phases in the DevSecOps ecosystem where the security process will be part of the entire life cycle:
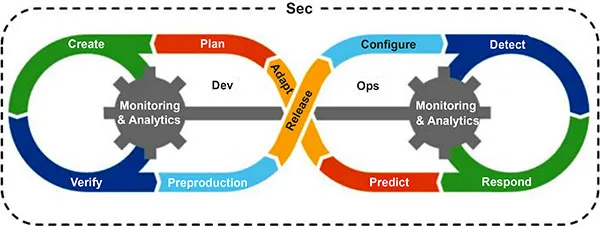
Figure 1.2: DevSecOps life cycle
With the final result of this pipeline, the requirements specification phase, and the implementation, configuration, and deployment of all the tools involved, we can execute the complete DevSecOps cycle, securing each of the phases with specific tools and integrating the entire process with continuous feedback in each phase.
The main benefits of this new culture of operations, development, and security are:
- More automation up front reduces the chances of mismanagement and lowers errors.
- According to Gartner, “DevSecOps can lead to security functions such as Identity and Access Management (IAM), firewall, and vulnerability scanning being programmatically enabled throughout the DevOps lifecycle, leaving security teams free to establish policies.”
- Security incidents are reduced and security is improved through shared responsibility between all teams.
- Vulnerability remediation costs are reduced.
When we integrate security into the development process instead of a layer that’s added later, we allow the power of agile methodologies to be harnessed by DevOps and security professionals with the aim of avoiding blocks to generate secure code.
ShiftLeft security
DevSecOps practice consists of including security in DevOps to adopt the good practices and benefits that the latter offers in development processes. To do this, it proposes to carry out a security shift left, incorporating security practices from the earliest stages of the development cycle.
These practices begin with the training and awareness of developers, as well as the involvement of stakeholders, being essential to the commitment of all parties regarding the security of the software.
Security must be considered from the design phase to avoid delay in project delivery. To reconcile agility and security, the solution lies in implementing security from the beginning of the project and not after it is completed.
Integrating security into an agile development cycle should start as early as possible, that is, in the requirements definition phase. This approach, called Security Shift Left, includes an orientation toward the principle of the security approach, allowing the software development process to have a totally secure workflow at each stage of the project development cycle.
For this, it is necessar...
Table of contents
- Cover Page
- Title Page
- Copyright Page
- Dedication Page
- About the Author
- About the Reviewers
- Acknowledgements
- Preface
- Errata
- Table of Contents
- 1. Getting Started with DevSecOps
- 2. Container Platforms
- 3. Managing Containers and Docker Images
- 4. Getting Started with Docker Security
- 5. Docker Host Security
- 6. Docker Images Security
- 7. Auditing and Analyzing Vulnerabilities in Docker Containers
- 8. Managing Docker Secrets and Networking
- 9. Docker Container Monitoring
- 10. Docker Container Administration
- 11. Kubernetes Architecture
- 12. Kubernetes Security
- 13. Auditing and Analyzing Vulnerabilities in Kubernetes
- 14. Observability and Monitoring in Kubernetes
- Index
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.5M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1.5 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Implementing DevSecOps with Docker and Kubernetes by José Manuel Ortega Candel in PDF and/or ePUB format, as well as other popular books in Computer Science & Cyber Security. We have over 1.5 million books available in our catalogue for you to explore.