- 258 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
Penetration Testing Bootcamp
About this book
Sharpen your pentesting skill in a bootcampAbout This Book• Get practical demonstrations with in-depth explanations of complex security-related problems• Familiarize yourself with the most common web vulnerabilities• Get step-by-step guidance on managing testing results and reportingWho This Book Is ForThis book is for IT security enthusiasts and administrators who want to understand penetration testing quickly.What You Will Learn• Perform different attacks such as MiTM, and bypassing SSL encryption• Crack passwords and wireless network keys with brute-forcing and wordlists• Test web applications for vulnerabilities• Use the Metasploit Framework to launch exploits and write your own Metasploit modules• Recover lost files, investigate successful hacks, and discover hidden data• Write organized and effective penetration testing reportsIn DetailPenetration Testing Bootcamp delivers practical, learning modules in manageable chunks. Each chapter is delivered in a day, and each day builds your competency in Penetration Testing.This book will begin by taking you through the basics and show you how to set up and maintain the C&C Server. You will also understand how to scan for vulnerabilities and Metasploit, learn how to setup connectivity to a C&C server and maintain that connectivity for your intelligence gathering as well as offsite processing. Using TCPDump filters, you will gain understanding of the sniffing and spoofing traffic. This book will also teach you the importance of clearing up the tracks you leave behind after the penetration test and will show you how to build a report from all the data obtained from the penetration test.In totality, this book will equip you with instructions through rigorous tasks, practical callouts, and assignments to reinforce your understanding of penetration testing.Style and approachThis book is delivered in the form of a 10-day boot camp style book. The day-by-day approach will help you get to know everything about penetration testing, from the use of network reconnaissance tools, to the writing of custom zero-day buffer overflow exploits.
Tools to learn more effectively

Saving Books

Keyword Search

Annotating Text

Listen to it instead
Information
Web Application Attacks
- Injection
- Broken authentication and session management
- XSS
- Broken access control
- Security misconfiguration
- Sensitive data exposure
- Insufficient attack protection
- Cross-site request forgery
- Using components with known vulnerabilities
- Under protected API's
- Manipulation by client-side testing
- Infrastructure and design weaknesses
- Identity-based testing
- Validating data, error handling and logic
- Session management
Manipulation by client-side testing
Cross-site scripting attacks
Reflected XSS attack


<script>alert("Your site is not protecting against XSS!Please fix ASAP!!")</script> 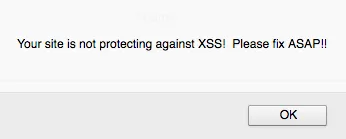
Stored XSS attack

Table of contents
- Title Page
- Copyright
- Credits
- About the Author
- About the Reviewer
- www.PacktPub.com
- Customer Feedback
- Preface
- Planning and Preparation
- Information Gathering
- Setting up and maintaining the Command and Control Server
- Vulnerability Scanning and Metasploit
- Traffic Sniffing and Spoofing
- Password-based Attacks
- Attacks on the Network Infrastructure
- Web Application Attacks
- Cleaning Up and Getting Out
- Writing Up the Penetration Testing Report
Frequently asked questions
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app