- 410 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
Enterprise Cloud Security and Governance
About this book
Build a resilient cloud architecture to tackle data disasters with ease
Key Features
- Gain a firm grasp of Cloud data security and governance, irrespective of your Cloud platform
- Practical examples to ensure you secure your Cloud environment efficiently
- A step-by-step guide that will teach you the unique techniques and methodologies of Cloud data governance
Book Description
Modern day businesses and enterprises are moving to the Cloud, to improve efficiency and speed, achieve flexibility and cost effectiveness, and for on-demand Cloud services. However, enterprise Cloud security remains a major concern because migrating to the public Cloud requires transferring some control over organizational assets to the Cloud provider. There are chances these assets can be mismanaged and therefore, as a Cloud security professional, you need to be armed with techniques to help businesses minimize the risks and misuse of business data.
The book starts with the basics of Cloud security and offers an understanding of various policies, governance, and compliance challenges in Cloud. This helps you build a strong foundation before you dive deep into understanding what it takes to design a secured network infrastructure and a well-architected application using various security services in the Cloud environment.
Automating security tasks, such as Server Hardening with Ansible, and other automation services, such as Monit, will monitor other security daemons and take the necessary action in case these security daemons are stopped maliciously. In short, this book has everything you need to secure your Cloud environment with. It is your ticket to obtain industry-adopted best practices for developing a secure, highly available, and fault-tolerant architecture for organizations.
What you will learn
- Configure your firewall and Network ACL
- Protect your system against DDOS and application-level attacks
- Explore cryptography and data security for your cloud
- Get to grips with configuration management tools to automate your security tasks
- Perform vulnerability scanning with the help of the standard tools in the industry
- Learn about central log management
Who this book is for
If you are a Cloud security professional who wants to ensure Cloud security and data governance irrespective of the environment, then this book is for you. Basic understanding of working on any Cloud platforms is beneficial.
Tools to learn more effectively

Saving Books

Keyword Search

Annotating Text

Listen to it instead
Information
Server Hardening
The basic principle of host-based security
- Only run the necessary services: This is one of the important aspects to follow. Only run services that are necessary and remove all the unnecessary services from the system. We also need to make sure that the services running do not have any security vulnerabilities associated with them.
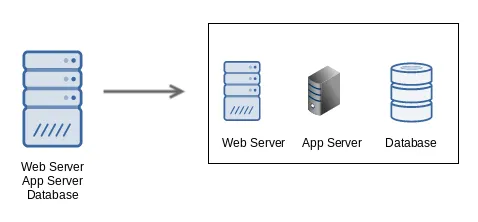
- Separate server by function: This is a mandatory requirement for PCI DSS. It mandates that each server should serve a single purpose. If you have a single large server to manage your workload and if it gets compromised, then all services within this server will be compromised.
- The principle of least privilege: Many system administrators assume that the principle of least privilege means that they should only give access to users who have a valid business requirement of the server. However, when we talk about enterprise-grade security, it is not just about users; even the process should be properly confined.
- Only allow users to run a command, which they need to complete the work.
- A developer wants to access an application server to check the logs. In order to check the logs, he would typically need commands, such as less, tail, and vim. In such cases, he should only be able to run commands such as tail and vim and should not be able to run commands such as netstat, getent passwd, or netstat -ntlp.
- In a Linux system, a user with even basic login privileges will be able to run commands, such as getent passwd or netstat. This becomes more challenging especially if there are any executables with the SetUID bit set. We will discuss in detail about SetUID in the upcoming section.
$ test-user@kplabs : getent passwd
root:x:0:0:root:/root:/bin/bash
arun:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
elasticsearch:x:120:130::/home/elasticsearch:/bin/false
zeal:x:1002:1002::/home/zeal:
manoj:x:1003:1003::/home/zeal:
- Restrictions on process access to files: You are running Apache as a web server, which serves the files from the /var/www/html folder. As a principle of least privilege, the process of Apache should only be able to access the /var/www/html directory and has no need to access all the other directories, such as /home or /root. Appropriate restrictions should be applied to ensure this.
Keeping systems up-to-date
The Windows update methodology
- Critical updates
- Security update
- Definition update
- Feature pack
The Linux update methodology
httpd-2.4.6-45.el7.centos.4.x86_64.rpm
Package name : httpd
Package Version : 2.4.6-45
OS : el7
Hardware Architecture : x86_64
Table of contents
- Title Page
- Copyright
- Credits
- About the Author
- About the Reviewer
- www.PacktPub.com
- Customer Feedback
- Preface
- The Fundamentals of Cloud Security
- Defense in Depth Approach
- Designing Defensive Network Infrastructure
- Server Hardening
- Cryptography Network Security
- Automation in Security
- Vulnerability, Pentest, and Patch Management
- Security Logging and Monitoring
- First Responder
- Best Practices
Frequently asked questions
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app